Digital Signs Add Cameras, Multiply Security Risks
The research is very clear—active digital signage can increase sales. With their large display areas, 4K colors, and user interactivity, they can be quite appealing. But as with any device connected to the Internet, security is a key concern. The ramifications of getting hacked range from simple nuisance to full-blown loss of corporate data.
Some digital signs employ a business model that includes revenue from advertising. Advertisers need to trust that their content is being displayed properly. If audience detection is in place, advertisers need to be sure that an unauthorized program hasn't altered the detection algorithms, miscounting the number of impressions, for example.
Many server vendors, including Kontron, like to employ a three-level architecture in the design of a digital sign. As shown in Figure 1, those levels would be application level, operating-system (OS) level, and firmware level, which includes the BIOS.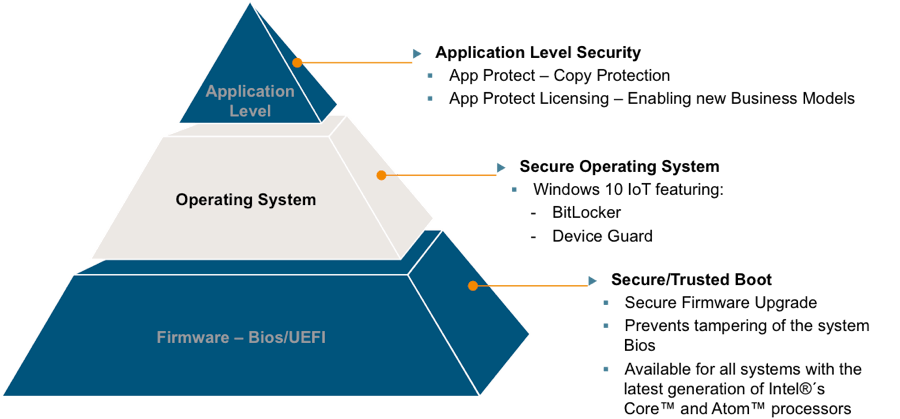
Figure 1. Kontron integrates security for digital signs at the BIOS, operating-system, and application levels.
Starting from the bottom up, Kontron's Secure/Trusted Boot offers a way to provide secure firmware updates and a protected boot mechanism. This is handled through an encrypted Trusted Platform Module (TPM), an international standard for hardware, currently in Version 2.0. This technique ensures that only programs that have been signed and verified are run during the boot process. Unauthorized and potentially harmful code would be rooted out here, including unwanted changes to the BIOS or the operating-system loader.
Moving up to the next level, the operating system, our design example takes advantage of Windows 10 IoT. Kontron is currently providing a secure version of the popular OS, Windows 10 IoT Long Term Servicing Branch (LTSB), a variant developed specifically for IoT environments, such as digital signage. It contains security mechanisms for the OS itself and for safeguarding data. This is achieved through integrated features, such as Secure Boot, BitLocker, Device Guard, and Credential Guard.
Finally, at the application level, Kontron relies on its APPROTECT security solution, which combines a software framework, an integrated security chip, and the TPM 2.0 for complete protection. APPROTECT encrypts an application’s source code in a way that makes reverse engineering nearly impossible. The integrated security chip constantly checks the application encryption to ensure that it's run only on the intended devices. At the same time, its integrity is monitored and protected to prevent manipulated applications from running.
SMARC Modules Add CSI
The processing and security solution required to build and secure a digital signage solution is available off-the-shelf, allowing signage developers to focus on adding value through great signage applications. One such example is the Kontron SMARC-sXAL module based on Intel's Atom® E3900 processor series. SMARC is an open standard form factor, overlapping in market focus with the well-known COM Express module standard. SMARC adds camera support with one or more MIPI-CSI interfaces enabling business models for digital signs based on visual processing.
The Intel Atom E3900 contains a variety of security features that enhance application security: It supports AES instructions, which improve the execution speed of encryption and decryption algorithms, and also offers Intel® Identity Protection Technology. This technology provides applications with a built-in security token used to verify the identity of a client system. To strengthen software-based security, the Atom E3900 supports a digital random number generator used as a seed in software algorithms.
The Camera Serial Interface (CSI) is a specification developed by the MIPI Alliance that defines an interface between a camera and a host processor. It enables frame resolutions of 1080p, 4k, 8k, and beyond, and stable images including 240 frames per second and higher. It also supports sensor fusion allowing camera imagery to be associated with ambient light, infrared, gyro, motion/presence detection, accelerometer, and MEMS sensors.
Three-Level Security
SMARC-sXAL supports secure/trusted boot at the Bios/UEFI level. This Intel feature establishes a root of trust on which higher applications can be run securely. SMARC-sXAL runs Windows 10 IoT, a secure operating system specifically developed for IoT cloud applications. Application trust is enhanced on Kontron modules using a technology called AppProtect, which offers copy protection and reverse-engineering protection with hardware-based encryption. AppProtect protects the screen and camera by refusing to run applications when the system is compromised with unauthorized code.
Foundation for Security
From trusted boot to faster encryption, security supported at all levels of application execution stands the best chance of resisting attack. Adding cameras to digital signs has provided another potential point of attack, but security measures used with the BIOS/UEFI, operating-system, and application software can help digital signs manage these risks.